I’m trying to setup SSO with SAML on Enterprise Trial.
My company’s Idp requires sending in Service Provider Metadata or Metadata URL.
How can I get it?
Before I’ve setup Tableau SAML with no probleam. (They provide the metadata info in Admin UI.)
Hi @heaven424
Which IdP are you using?
The “SAML metadata” is normally just a JSON file, which includes the same information as Metabase asks for in separate fields.
I have a SAML metadata template from Tableau.
Can I just fill in the template below, and use it for metabase?
I made X509 certificate using openssl for test purposes.
<?xml version="1.0" encoding="UTF-8"?>
<md:EntityDescriptor xmlns:md="urn:oasis:names:tc:SAML:2.0:metadata" ID="http://test.example.com" entityID="http://test.example.com">
<md:SPSSODescriptor AuthnRequestsSigned="true" WantAssertionsSigned="true" protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol">
<md:KeyDescriptor use="signing">
<ds:KeyInfo xmlns:ds="http://www.w3.org/2000/09/xmldsig#">
<ds:X509Data>
<ds:X509Certificate>
Certificate Here...
</ds:X509Certificate>
</ds:X509Data>
</ds:KeyInfo>
</md:KeyDescriptor>
<md:KeyDescriptor use="encryption">
<ds:KeyInfo xmlns:ds="http://www.w3.org/2000/09/xmldsig#">
<ds:X509Data>
<ds:X509Certificate>
Certificate Here...
</ds:X509Certificate>
</ds:X509Data>
</ds:KeyInfo>
</md:KeyDescriptor>
<md:NameIDFormat>urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress</md:NameIDFormat>
<md:NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:transient</md:NameIDFormat>
<md:NameIDFormat>urn:oasis:names:tc:SAML:2.0:nameid-format:persistent</md:NameIDFormat>
<md:NameIDFormat>urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified</md:NameIDFormat>
<md:NameIDFormat>urn:oasis:names:tc:SAML:1.1:nameid-format:X509SubjectName</md:NameIDFormat>
<md:AssertionConsumerService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="http://test.example.com/wg/saml/SSO/index.html" index="0" isDefault="true"/>
</md:SPSSODescriptor>
</md:EntityDescriptor>@heaven424 Not sure what you’re asking, but you cannot use “SAML metadata as a JSON file”. You need to input the values in the appropriate fields in Metabase.
https://www.metabase.com/docs/latest/enterprise-guide/authenticating-with-saml.html
I know that SAML setting in metabase requires filling in the admin UI. The json file is for registering SP to company IdP.
@heaven424 It’s the same information. One is in a file, Metabase uses separated inputs.
Otherwise I don’t understand what you mean, but I don’t know which IdP you’re using, so it’s difficult to help. Metabase support at least 10 of the biggest IdP services and systems.
Somewhat I managed to get registred with Idp Provider, and changed some user attributes settings.
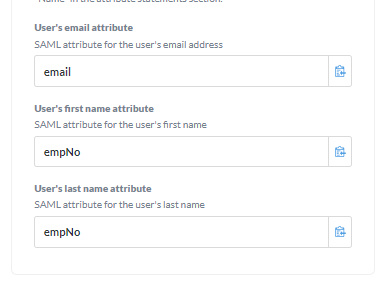
My IdP does not have first name and last name attributes, so it was replaced with employ number attribute.
Now I can see the login page for single sign-on,
but after logging in, I get back to the Metabase Sign-in page.
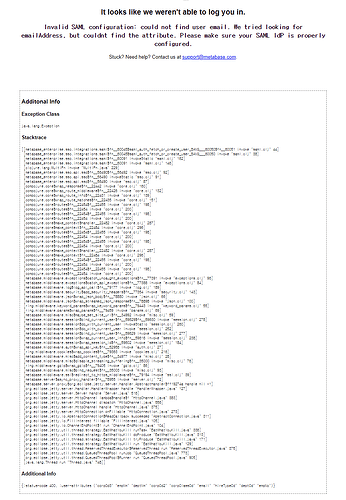
I see errors as below as each time I try to login : (from server/admin/troubleshooting/logs)
[89f9a809-908d-41c0-b4e6-cafa12b20198] 2021-02-17T18:06:47+09:00 DEBUG metabase.middleware.log GET /api/user/current 401 165.4 µs (0 DB calls)
"Unauthenticated"[89f9a809-908d-41c0-b4e6-cafa12b20198] 2021-02-17T18:06:47+09:00 DEBUG metabase.middleware.log GET /api/session/properties 200 4.3 ms (0 DB calls) App DB connections: 0/10 Jetty threads: 5/50 (1 idle, 0 queued) (105 total active threads) Queries in flight: 0 (0 queued)
[89f9a809-908d-41c0-b4e6-cafa12b20198] 2021-02-17T18:06:53+09:00 DEBUG metabase.middleware.log GET /api/user/current 401 138.1 µs (0 DB calls)
"Unauthenticated"[89f9a809-908d-41c0-b4e6-cafa12b20198] 2021-02-17T18:06:53+09:00 DEBUG metabase.middleware.log GET /api/session/properties 200 4.5 ms (0 DB calls) App DB connections: 0/10 Jetty threads: 5/50 (1 idle, 0 queued) (105 total active threads) Queries in flight: 0 (0 queued)
[89f9a809-908d-41c0-b4e6-cafa12b20198] 2021-02-17T18:06:57+09:00 DEBUG metabase.middleware.log GET /api/user/current 401 153.6 µs (0 DB calls)
"Unauthenticated"
On the user admin page, my information was updated with attributes from the IdP.
Do you have any guess why Metabase is sending 401 response?
Or is there someway I can get more detailed log on the saml failures?
- Post “Diagnostic Info” from Admin > Troubleshooting
- Which IdP are you using?
My company has own implementation SAML2.0 to provide SSO service throughout in-house platforms.
I guess it's not specific to one of the providers on the document.
Diagnositc Info from the test browser is as below:
{
"browser-info": {
"language": "ko-KR",
"platform": "Win32",
"userAgent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.150 Safari/537.36",
"vendor": "Google Inc."
},
"system-info": {
"file.encoding": "UTF-8",
"java.runtime.name": "OpenJDK Runtime Environment",
"java.runtime.version": "1.8.0_151-b12",
"java.vendor": "Oracle Corporation",
"java.vendor.url": "http://java.oracle.com/",
"java.version": "1.8.0_151",
"java.vm.name": "OpenJDK 64-Bit Server VM",
"java.vm.version": "25.151-b12",
"os.name": "Linux",
"os.version": "2.6.32-696.13.2.el6.x86_64",
"user.language": "en",
"user.timezone": "ROK"
},
"metabase-info": {
"databases": [
"h2"
],
"hosting-env": "unknown",
"application-database": "h2",
"application-database-details": {
"database": {
"name": "H2",
"version": "1.4.197 (2018-03-18)"
},
"jdbc-driver": {
"name": "H2 JDBC Driver",
"version": "1.4.197 (2018-03-18)"
}
},
"run-mode": "prod",
"version": {
"tag": "v1.37.9",
"date": "2021-02-11",
"branch": "release-x.37.x",
"hash": "a9a7fc8"
},
"settings": {
"report-timezone": "Asia/Seoul"
}
}
}
When I change the email attribute name to something else,
I get metabase error message after login :
I guess setting it to "email" is working, but now I get back to the login page.
Okay, I’m not seeing any requests to /auth/sso - does your IdP return to that address?
It’s extremely important that the Site URL is configured correctly in Admin > Settings > General.
You’re seeing the 401 because the user hasn’t been authenticated.
And are you doing login via normal in-app or via FullApp Embedding?
You can use your browser developer Network-tab to see the requests during the SAML authentication.
There’s also extensions like this, which can help: https://chrome.google.com/webstore/detail/saml-chrome-panel/paijfdbeoenhembfhkhllainmocckace
I’m testing on in-app mode, but we hope to use it in FullApp embedding.
Here is how the SAML response from the IdP after login looks like.
<?xml version="1.0" encoding="UTF-8"?>
<saml2p:Response Destination="http://test.example.com:3000/auth/sso"
ID="_1e065b68-1e04-48c5-8953-70cd0376bc63" InResponseTo="id-a9a2447f-2ed7-4f86-9117-99a1385fdc64"
IssueInstant="2021-02-18T01:28:45.319Z" Version="2.0"
xmlns:saml2p="urn:oasis:names:tc:SAML:2.0:protocol" xmlns:xs="http://www.w3.org/2001/XMLSchema">
<saml2:Issuer Format="urn:oasis:names:tc:SAML:2.0:nameid-format:entity"
xmlns:saml2="urn:oasis:names:tc:SAML:2.0:assertion">saml-test</saml2:Issuer>
<ds:Signature xmlns:ds="http://www.w3.org/2000/09/xmldsig#">
<ds:SignedInfo><ds:CanonicalizationMethod Algorithm="http://www.w3.org/2001/10/xml-exc-c14n#"/><ds:SignatureMethod Algorithm="http://www.w3.org/2000/09/xmldsig#rsa-sha1"/>
<ds:Reference URI="#_1e065b68-1e04-48c5-8953-70cd0376bc63">
<ds:Transforms><ds:Transform Algorithm="http://www.w3.org/2000/09/xmldsig#enveloped-signature"/>
<ds:Transform Algorithm="http://www.w3.org/2001/10/xml-exc-c14n#"><ec:InclusiveNamespaces PrefixList="xs" xmlns:ec="http://www.w3.org/2001/10/xml-exc-c14n#"/></ds:Transform>
</ds:Transforms><ds:DigestMethod Algorithm="http://www.w3.org/2000/09/xmldsig#sha1"/>
<ds:DigestValue>qjgZwXbPeeKFe/IMeYNdzq890YY=</ds:DigestValue>
</ds:Reference>
</ds:SignedInfo>
<ds:SignatureValue>Some Signature Here</ds:SignatureValue>
<ds:KeyInfo>
<ds:X509Data>
<ds:X509Certificate>IdP Certificate Here</ds:X509Certificate>
</ds:X509Data>
</ds:KeyInfo>
</ds:Signature>
<saml2p:Status><saml2p:StatusCode Value="urn:oasis:names:tc:SAML:2.0:status:Success"/></saml2p:Status>
<saml2:Assertion ID="_8bb56187-69a6-4c68-b403-d37e6fdf986f" IssueInstant="2021-02-18T01:28:45.319Z"
Version="2.0" xmlns:saml2="urn:oasis:names:tc:SAML:2.0:assertion"
xmlns:xs="http://www.w3.org/2001/XMLSchema">
<saml2:Issuer Format="urn:oasis:names:tc:SAML:2.0:nameid-format:entity">saml-test</saml2:Issuer>
<ds:Signature xmlns:ds="http://www.w3.org/2000/09/xmldsig#">
<ds:SignedInfo><ds:CanonicalizationMethod Algorithm="http://www.w3.org/2001/10/xml-exc-c14n#WithComments"/><ds:SignatureMethod Algorithm="http://www.w3.org/2000/09/xmldsig#rsa-sha1"/>
<ds:Reference URI="#_8bb56187-69a6-4c68-b403-d37e6fdf986f">
<ds:Transforms><ds:Transform Algorithm="http://www.w3.org/2000/09/xmldsig#enveloped-signature"/>
<ds:Transform Algorithm="http://www.w3.org/2001/10/xml-exc-c14n#"><ec:InclusiveNamespaces PrefixList="xs" xmlns:ec="http://www.w3.org/2001/10/xml-exc-c14n#"/></ds:Transform>
</ds:Transforms><ds:DigestMethod Algorithm="http://www.w3.org/2000/09/xmldsig#sha1"/>
<ds:DigestValue>1K94G06NF4C9vPL8NcMEIUxRVG8=</ds:DigestValue>
</ds:Reference>
</ds:SignedInfo>
<ds:SignatureValue>Signature Here</ds:SignatureValue>
</ds:Signature>
<saml2:Subject>
<saml2:NameID Format="urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress">dev-empno@example.com</saml2:NameID>
<saml2:SubjectConfirmation Method="urn:oasis:names:tc:SAML:2.0:cm:bearer"><saml2:SubjectConfirmationData InResponseTo="id-a9a2447f-2ed7-4f86-9117-99a1385fdc64"
NotOnOrAfter="2021-02-18T01:38:45.319Z" Recipient="http://test.example.com:3000/auth/sso"/></saml2:SubjectConfirmation>
</saml2:Subject>
<saml2:Conditions NotBefore="2021-02-18T01:18:45.319Z" NotOnOrAfter="2021-02-18T01:38:45.319Z">
<saml2:AudienceRestriction>
<saml2:Audience>Metabase</saml2:Audience>
</saml2:AudienceRestriction>
</saml2:Conditions>
<saml2:AuthnStatement AuthnInstant="2021-02-18T01:28:45.319Z"
SessionIndex="_8bb56187-69a6-4c68-b403-d37e6fdf986f">
<saml2:AuthnContext>
<saml2:AuthnContextClassRef>urn:oasis:names:tc:SAML:2.0:ac:classes:Password</saml2:AuthnContextClassRef>
<saml2:AuthenticatingAuthority>saml-test</saml2:AuthenticatingAuthority>
</saml2:AuthnContext>
</saml2:AuthnStatement>
<saml2:AttributeStatement>
<saml2:Attribute Name="deptCd" NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:unspecified">
<saml2:AttributeValue xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:type="xs:string">XXXXX</saml2:AttributeValue>
</saml2:Attribute>
<saml2:Attribute Name="deptNm" NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:unspecified">
<saml2:AttributeValue xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:type="xs:string">Dev</saml2:AttributeValue>
</saml2:Attribute>
<saml2:Attribute Name="email" NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:unspecified">
<saml2:AttributeValue xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:type="xs:string">xxx@example.com</saml2:AttributeValue>
</saml2:Attribute>
<saml2:Attribute Name="empNm" NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:unspecified">
<saml2:AttributeValue xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:type="xs:string">XXX</saml2:AttributeValue>
</saml2:Attribute>
<saml2:Attribute Name="empNo" NameFormat="urn:oasis:names:tc:SAML:2.0:attrname-format:unspecified">
<saml2:AttributeValue xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xsi:type="xs:string">xxx</saml2:AttributeValue>
</saml2:Attribute>
</saml2:AttributeStatement>
</saml2:Assertion>
</saml2p:Response>@heaven424 Okay, I’m not sure what’s going wrong, but I don’t see your IdP returning to Metabase from the logs (/auth/sso).
You can try enabling debug logging:
https://www.metabase.com/docs/latest/operations-guide/log-configuration.html
I can see the response is slightly different from other IdPs, but since you’re using a custom IdP, then it’s not possible for me to check or validate anything.
Have you tried using a validator? Example https://www.samltool.com/validate_response.php
If that doesn’t work, then use the support email and supply screenshots of your SAML configuration in Metabase and the full logs - with less redaction.